Blog
HomeBlogPage 67
-
Apr 3, 2015
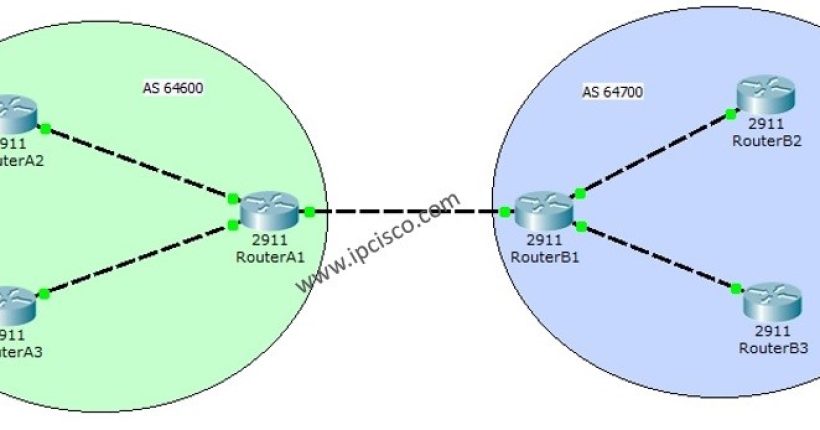
Packet Tracer BGP Configuration Example To understand BGP (Border Gateway Protocol) better, we will make a basic Packet Tracer BGP...
-
Apr 2, 2015
Ping Command and Ping Command Options Whenever other engineers see network engineers during troubleshooting, they think that, network engineers only...
-
Mar 30, 2015
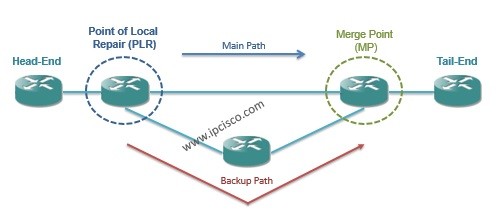
Both One-to-One and Facility Backup can protect different network elements. And these can be achieved by two ways: – Node...
-
Mar 30, 2015
The goal of the protection is minimizing the down time. To do this, protection must be done near to the...
-
Mar 30, 2015
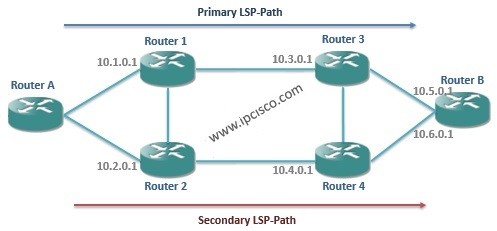
As we say in the following articles, while using Secondary LSP-Paths, sharing links between Primary and Secondary LSP-Paths must be...
Popular posts
Cisco Interview Questions
June 30, 2025
Cisco
Network Operating System
March 14, 2025
Basic
CCNA Minor Update! | CCNA 200-301 v1.1
July 9, 2024
Basic
Cisco Packet Tracer Overview
June 26, 2024
CCNA
Sign up to receive our latest updates
Get in touch
Call us directly?
+1 234 567 8910
Address
Howard Street, San Francisco
contact@eduma.com